The enactment of China’s latest security protocols for supply chain management represents a fundamental shift from market-driven efficiency to a state-managed risk mitigation architecture. While previous iterations focused on data sovereignty and cybersecurity, the current framework codifies the "fortress economy" model, designed to insulate domestic industrial bases from external geopolitical shocks and extraterritorial sanctions. This shift signifies that Beijing no longer views supply chain integration as a tool for growth, but as a primary vector of national vulnerability.
The Tripartite Architecture of Supply Chain Insulation
The new regulations operate across three distinct functional layers: systemic visibility, substitution mandates, and retaliatory elasticity. Each layer targets a specific failure point identified during the 2018–2024 period of trade friction and semiconductor restrictions.
1. Systemic Visibility and Information Control
The first pillar requires a granular mapping of upstream dependencies. Under the new rules, "critical industrial operators" must provide exhaustive documentation regarding the origin of components, software, and raw materials. This is not merely a compliance exercise; it is an intelligence-gathering operation to identify "choke points"—technologies where a single foreign entity holds a dominant market share.
By centralizing this data, the state can identify which domestic firms are most exposed to Western export controls before those controls are even enacted. This creates a preemptive defensive posture where the government can direct capital toward domestic alternatives for the most fragile nodes in the network.
2. The Substitution Mandate
The second pillar moves beyond observation into active intervention. The framework establishes a "domestic-first" procurement hierarchy for sectors labeled as vital to national security. This includes:
- Semiconductor manufacturing equipment: Focusing on mature node lithography and etching tools to ensure baseline industrial capacity.
- Industrial software (EDA/CAD): Reducing reliance on Western design suites that can be disabled remotely or via license revocation.
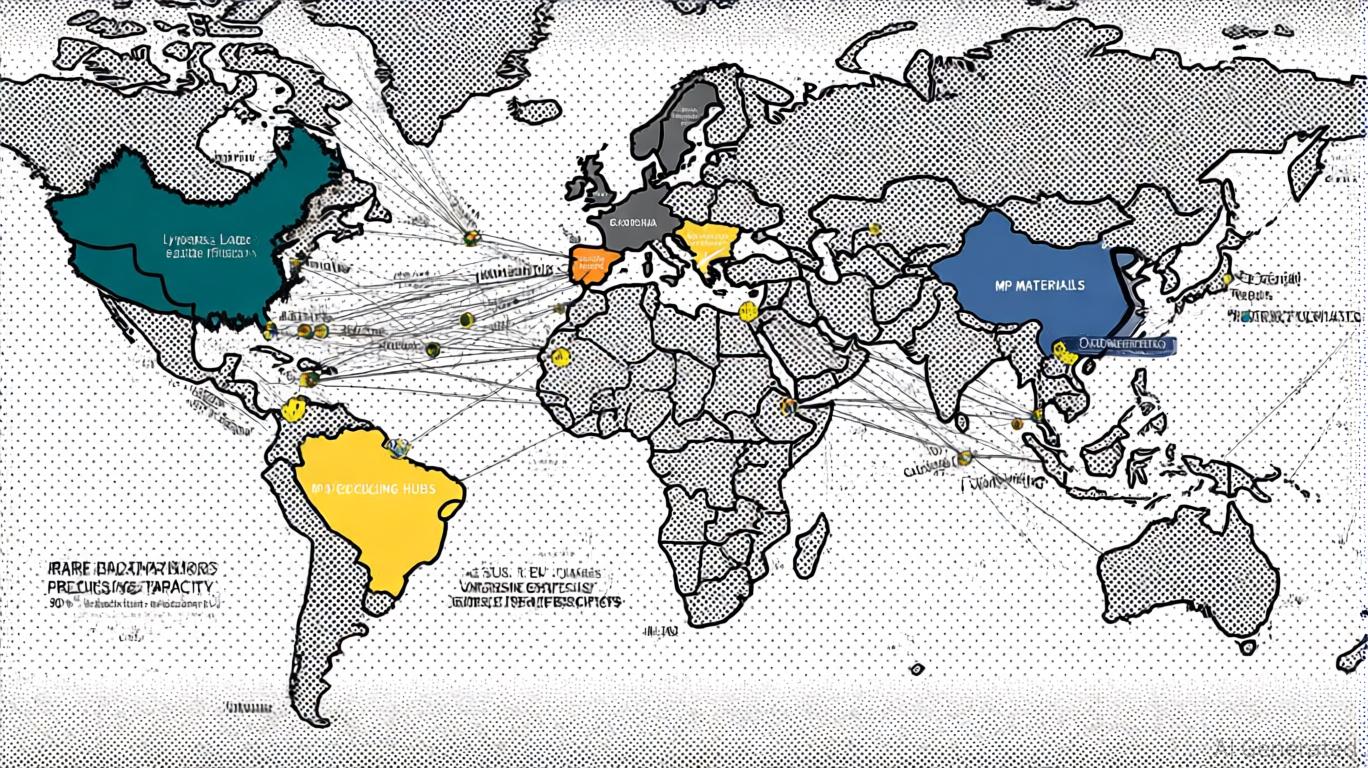
- Advanced materials: Securing the production of rare earth processing, specialized polymers, and high-grade alloys used in aerospace and defense.
This mandate functions as an internal subsidy, forcing domestic demand toward nascent Chinese suppliers, thereby providing them with the cash flow and operational data required to iterate toward parity with global leaders.
3. Retaliatory Elasticity
The third pillar introduces mechanisms for rapid response to foreign sanctions. The regulations provide a legal basis for the state to counter-sanction firms that comply with "unjustified" foreign trade restrictions. This places multinational corporations in an impossible position: comply with US export controls and risk losing access to the Chinese market, or comply with Chinese security rules and risk legal action in their home jurisdictions.
The Cost Function of Security-Centric Logistics
Prioritizing security over efficiency introduces a series of unavoidable economic frictions. The transition to a "fortress" model shifts the cost curve upward for all domestic manufacturers.
Capital Allocation Inefficiency
When the state dictates procurement based on security rather than performance or price, capital is diverted from high-ROI R&D into "reinventing the wheel." A Chinese firm forced to use a less efficient domestic chip designer spends more on power consumption and thermal management, which degrades the final product’s competitiveness in non-Chinese markets. This creates a "dual-track" industrial reality where Chinese products are optimized for domestic survival rather than global dominance.
The Innovation Bottleneck
Global supply chains act as a mechanism for knowledge transfer. By hardening the perimeter against foreign suppliers, China risks cutting off the informal flows of expertise—best practices, maintenance standards, and iterative feedback loops—that come with integrating "best-in-class" global components. The isolation of these systems can lead to "technological drift," where domestic standards diverge so far from global benchmarks that they become incompatible with the rest of the world.
The Mechanism of De-Risking in Reverse
The West’s strategy of "de-risking" focuses on reducing dependency on Chinese manufacturing. China’s new rules are the mirror image: reducing dependency on Western intellectual property and financial systems. This reciprocal isolation creates a feedback loop that accelerates the bifurcation of global trade.
We are seeing the emergence of two distinct "Technological Spheres of Influence." Each sphere operates on its own stack of hardware, software, and legal standards. For businesses operating in both, the cost of "interoperability" is becoming a prohibitive tax.
Data as a Strategic Asset
The framework treats industrial data with the same level of protection as classified military intelligence. The flow of operational data—such as manufacturing yields or logistics timestamps—is now restricted. For a global company, this means they can no longer maintain a "single pane of glass" view of their global operations. The Chinese subsidiary becomes a black box, integrated only through the narrowest of APIs, controlled by the state.
The Strategic Bottleneck: Semiconductor Lithography and EDA
The most significant test of this new security framework lies in the high-end semiconductor space. While China has successfully localized many parts of the assembly and packaging process, the "apex" technologies remain elusive.
The new rules attempt to bridge this gap by mandating "coordinated development" between state-owned enterprises (SOEs) and private tech giants. The goal is to create a closed-loop ecosystem where the SOEs provide the long-term capital and the private sector provides the engineering agility. However, the complexity of 3nm and 2nm manufacturing is not just a matter of capital; it is a matter of decades of accumulated tacit knowledge. The security framework provides the "will," but it cannot easily manufacture the "skill" in a vacuum.
Operational Realities for Multinational Corporations
For foreign firms, the "business as usual" era is officially over. The new regulations demand a fundamental restructuring of how these entities view their Chinese assets.
- Legal Localization: Companies are forced to move their legal and compliance functions into China, staffed by local nationals who can navigate the ambiguity of "national security" definitions without triggering foreign agent registration acts in their home countries.
- Technological Partitioning: Firms are increasingly building "In China, For China" (ICFC) product lines. These products are designed, sourced, and manufactured entirely within the Chinese perimeter to avoid the entanglement of the security framework. This results in the loss of scale economies, as the firm must now maintain two separate R&D pipelines.
- The Sovereignty Tax: Compliance with these rules represents a direct hit to margins. The administrative burden of mapping every sub-component and the risk of being caught in a crossfire of retaliatory sanctions acts as a permanent tax on doing business in the region.
The Shift from Just-in-Time to Just-in-Case
The global logistics model of the late 20th century was built on the assumption of frictionless borders and stable geopolitical conditions. China’s new security rules are the final nail in the coffin for that era. The new model is "Just-in-Case," characterized by redundant suppliers, localized manufacturing, and high inventory levels.
This transition is inflationary by nature. Redundancy costs money. Security costs money. The "peace dividend" that fueled the low-inflation growth of the 2000s has been traded for the "security dividend" of the 2020s.
Structural Implications for Global Trade
The broader implication is a shift toward "fragmented globalization." Trade volumes may not collapse, but the nature of that trade is changing. Instead of finished goods moving freely, we see the movement of intermediate goods between friendly nations ("friend-shoring") and the localization of final assembly.
China is positioning itself as the hub of a "non-Western" supply chain, courting partners in the Global South by offering a security-hardened industrial stack that is immune to US dollar-based sanctions. The new security rules are the "operating system" for this alternative trade network.
Strategic Action: The Perimeter Defense Model
To survive this transition, organizations must move beyond simple risk assessment and adopt a Perimeter Defense Model. This requires the immediate decoupling of critical data and IP from the Chinese operational environment while maintaining a localized "mirrored" infrastructure for domestic operations.
The primary objective is no longer growth at all costs, but the preservation of core intellectual property. If a component or process is essential to a firm’s global competitive advantage, it must be removed from the Chinese supply chain entirely. Conversely, if a product is intended for the Chinese market, it must be "indigenized" to the point where it can survive a total severance of international ties.
The goal is to reach a state of "controlled optionality"—the ability to maintain operations in China if conditions are stable, but to "sever the link" instantly and cleanly if the geopolitical environment necessitates a total exit. Any firm that cannot execute a clean break within 96 hours is currently over-leveraged to a system that is actively hardening its shell against them.